Internet browsing and emails, mobile applications, online payment services, storage in the cloud, the use of wearables or the Internet of Things revolution… The technology boom of recent years has changed our lives forever. But good things have a price. And in this case the price to pay is the security of our data and our privacy.
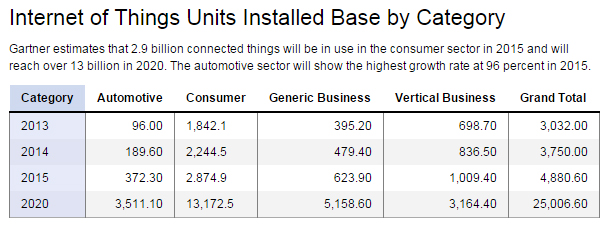
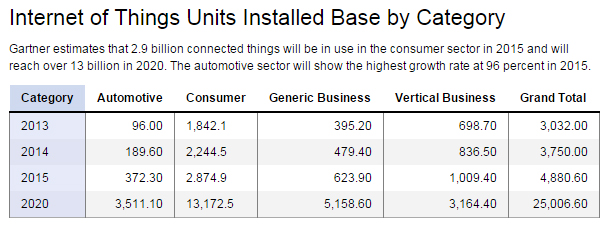
A recent study by Hewlett Packard showed that 70% of the Internet of Things (IoT) devices have security vulnerabilities in the passwords, encryption or user access permissions. In a business of 263,000 million dollars in revenue and more than 25 billion devices connected by 2020, cybersecurity is a priority. Here you can see the progression in the growth of IoT devices, according to a study by Gartner:
Manufacturers are quickly launching to market their IoT devices and wearables to meet consumer demand, but at the expense of a greater weakness in software development and increased security threats: either companies invest money and time on cybersecurity, or 'machine to machine' (M2M) will be a breeding ground for distributed denial of service (DDoS) attacks, attacks on passwords, and vulnerabilities such as cross-site scripting.
Business and work opportunities for developers
For all these reasons, investment plans in cybersecurity are going to provide business and employment opportunities for developers and entrepreneurs in 2015. Companies and authorities around the planet are establishing legal protocols to make cyberspace a safe haven. In fact, security will be a flourishing business because there is also a large projection on the 'dark side of the force'. How many developers use their knowledge to trade with third party information extracted from wearables, Internet of Things devices, emails or mobile applications?
More and more companies use online devices to manage professional documentation, save costs, increase productivity… and much of the data of those devices is a gold mine for hackers willing to trade with this type of sensitive information.
In fact, according to figures from the National Cryptologic Centre (CCN) of the Spanish National Intelligence Center (CNI), almost all large companies and 58% of Spanish SMEs suffered any of the 7,263 computer attacks registered in Spain in 2013, 82% more than in 2012. As time passes, the IoT and wearables will become a technology accessible to all and the risk of threats and leakage of private information will be enormous.
Sogeti and IBM estimate that the cybersecurity-related business will grow 10% annually until 2017 and that its turnover is currently around 32 billion euros, a figure really ridiculous if we compare it with the 390 billion euros of losses generated by computer attacks on companies and organizations worldwide. Clearly, it is cheaper to invest in security.
Investment of the large Spanish and international companies
Technology services companies such as Cisco are already promoting small startups or projects dedicated to the IoT and, particularly, to security aspects in this field. In mid-October, the company announced the winners of the Cisco Internet of Things Grand Challenges. Among them was the Excalibur Group project, which has designed a new security system for the Internet of Things based on blockchains and sensitivity to the context. Projects from Rice University and Carnegie Mellon University and institutions such as the Max Planck Institute were also awarded.
The technology consulting firm Indra created over a year and a half ago a center dedicated exclusively to cybersecurity, called i-CSOC (CyberSecurity Operations Centre), which serves businesses, institutions and governments throughout the year. Indra employs over 100 people in the i-CSOC, in a space of 500 square meters, totally shielded from radiation and with safety certificate, which is serving some Defense ministries of NATO countries.
Another company that has shown great interest in the business of cybersecurity is Telefónica. In fact, the telecom operator has reported 75 million euros in revenues during the first three quarters of 2014 related to Information Security tasks, with an inter-annual growth of 42%. Two of its current projects are Sinfonier, a free community dedicated to cybersecurity developers, and a new subsidiary, Telefónica Digital Identity & Privacy, launched in cooperation with the company Eleven Paths, founded by the popular hacker Chema Alonso.
Deloitte also is moving very strongly in this sector. Its Cybersecurity Operations Center (CyberSOC) is a reference organization in Spain.
Laws against ciberwarriors
For more than two years there have been discussions about the possible consequences of a 'Cyber-11s' in the world of communications, with terrorist attacks without bombs, but with similar results. Attacks of 'ciberwarriors' who with the use of technology were able to, for example, take down the national stocks or powerful companies… This is something that, with the Internet of Things and wearable devices with professional use, can become a very real nightmare.
For José María de Fuentes, Lorena González Manzano and Arturo Ribagorda Garnacho, Cybersecurity professors at the Carlos III University, the advances that are being made by the different administrations are crucial. Spain adopted one year ago the Strategy of National Cybersecurity (ECN), while the US has in place the Defense Advanced Research Projects Agency (DARPA), which has funded research programs as CINDER (Cyber Insider Threats) and ADAMS (Anomaly Detection at Multiple Scales).
“It is true that the multiple news we see in all types of media may lead people to think that cybersecurity is an instrument of espionage and control”, say De Fuentes, González and Ribagorda, “but its goal is to provide the means to fight against emerging threats.” Consumers need professionals to improve the safety of the devices that they will use in the future, such as a mobile phone or a computer.